
Image from Miha Creative
Hello AWS users,
We here at doit.com are writing this post to bring your attention to an important security update from Amazon Web Services (AWS) regarding the Elastic Container Service (ECS). This update specifically affects some AWS users who have been notified in their AWS Health Dashboard under Other notifications.
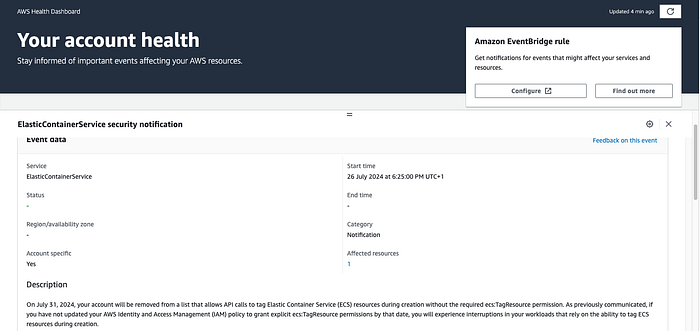
Security Notification from AWS Health Dashboard
You can check your notifications here.
Starting from today 31st July 2024, AWS will require the ecs:TagResource permission for making API calls that tag ECS resources during creation. This change, initially introduced on 18th April 2023, is designed to give AWS customers more control over the tagging of ECS resources.
Affected APIs
This change will affect the following APIs:
- CreateCapacityProvider
- CreateCluster
- CreateService
- CreateTaskSet
- RegisterContainerInstance
- RegisterTaskDefinition
- RunTask
- StartTask
What Happens If You Don’t Update?
If your IAM policy does not include the ecs:TagResource permission, you will receive an AccessDeniedException when making ECS API calls with tags. This could potentially interrupt your workloads that rely on the ability to tag ECS resources during creation.
For instance, if you have an IAM policy that grants the ecs:CreateCluster permission to all resources but does not include the ecs:TagResource action, you would encounter an error when trying to create a cluster with tags. Here's an example:
{
"Version": "2012-10-17",
"Statement": [\
{\
"Sid": "AllowCreateCluster",\
"Effect": "Allow",\
"Action": [\
"ecs:CreateCluster"\
],\
"Resource": "*"\
}\
]
}
If you run the following Create Cluster Request:
aws ecs create-cluster --cluster-name MyCluster --tags key=key1,value=value1
You would receive this Tagging Denied Response:
An error occurred (AccessDeniedException) when calling the CreateCluster operation:
User: is not authorized to perform: ecs:TagResource on resource: cluster/MyCluster because no identity-based policy allows the ecs:TagResource action
How to fix? Update Your IAM Policy
To prevent this, you should update your IAM policy to explicitly allow the ecs:TagResource action. Here's an example of how to update your IAM policy:
"Statement": [\
{\
"Sid": "AllowCreateCluster",\
"Effect": "Allow",\
"Action": [ "ecs:CreateCluster" ],\
"Resource": "*"\
},\
{\
"Sid": "AllowTagging",\
"Effect": "Allow",\
"Action": [ "ecs:TagResource" ],\
"Resource": "*"\
}\
]
This update will ensure that ECS API calls with tag-on-create continue to succeed on or after July 31, 2024.
As the change comes into affect today for affected AWS users, we strongly recommend you update your IAM policies to avoid any interruptions.
We hope this post has been helpful. If you have any questions or need further clarification, feel free to reach out to us here at doit.com