DoiT Cloud Intelligence™
Fine-Grained Outbound Control: How Google Cloud Cloud NAT Rules Enhance Security and Compliance

Google Cloud Network Address Translation ( Cloud NAT) is a key service that enables Virtual Machines (VMs) without external IP addresses (private VMs) to securely connect to the internet. This allows private VMs to securely receive software updates, access external APIs, and utilize other external services while remaining isolated from inbound internet connections.
By default, Cloud NAT handles outbound traffic efficiently by translating the internal source IP address of a VM to one of the public NAT IP addresses assigned to the gateway. However, in modern cloud architectures, efficiency is not enough. Organizations need policy-driven control over outbound traffic. This is where Cloud NAT rules come into play. They transform Cloud NAT from a basic translation service into a sophisticated policy enforcement point for outbound connectivity, allowing for explicit control over which public IP address is used for which traffic flow.
Challenges Without Cloud NAT Rules
In a standard Cloud NAT setup, all outbound traffic from a VPC shares the same pool of public IP addresses. While simple, this creates several issues in complex or regulated environments:
- Strict Whitelisting Issues: Many critical external services like payment processors, partner APIs, and security systems enforce strict firewall policies, requiring whitelisting of specific public IPs. Without rules, your private VMs would use rotating or shared IPs, forcing whitelisting of all or risking connection failures.
- Lack of Traffic Segmentation: All internet-bound traffic looks the same to the outside world. There’s no way to easily segment or audit for a specific purpose.
- Audit and Compliance Gaps: In regulated industries, outbound connections must sometimes be traced back to specific applications or environments. When all traffic uses a unified IP pool, this traceability is lost on the public internet, complicating audit trails and regulatory compliance.
How NAT Rules Solve These Problems
Cloud NAT rules solve these problems by introducing conditional logic to the NAT process. A rule defines a match condition (based on source or destination) and a corresponding action (which specific NAT IP address to use). Once NAT rules are defined, each packet is tested against them. If a packet meets the condition of a rule, the specified action is executed.
The key solutions offered by Cloud NAT rules are (Only IPv4 destination addresses are supported):
Source-Based Traffic Segmentation ( Preview): In source-based rules, packets are matched by their source IP address ( the internal IP range of a specific subnet).
“IF the traffic is coming from the
10.10.20.0/24subnet (our testing environment), THEN use the public NAT IP203.0.113.50."
This is invaluable for traffic segmentation. It allows you to assign a dedicated, easily identifiable public IP to specific applications, environments (like Dev/Test/Prod), or high-priority subnets, making auditing and security monitoring significantly easier.
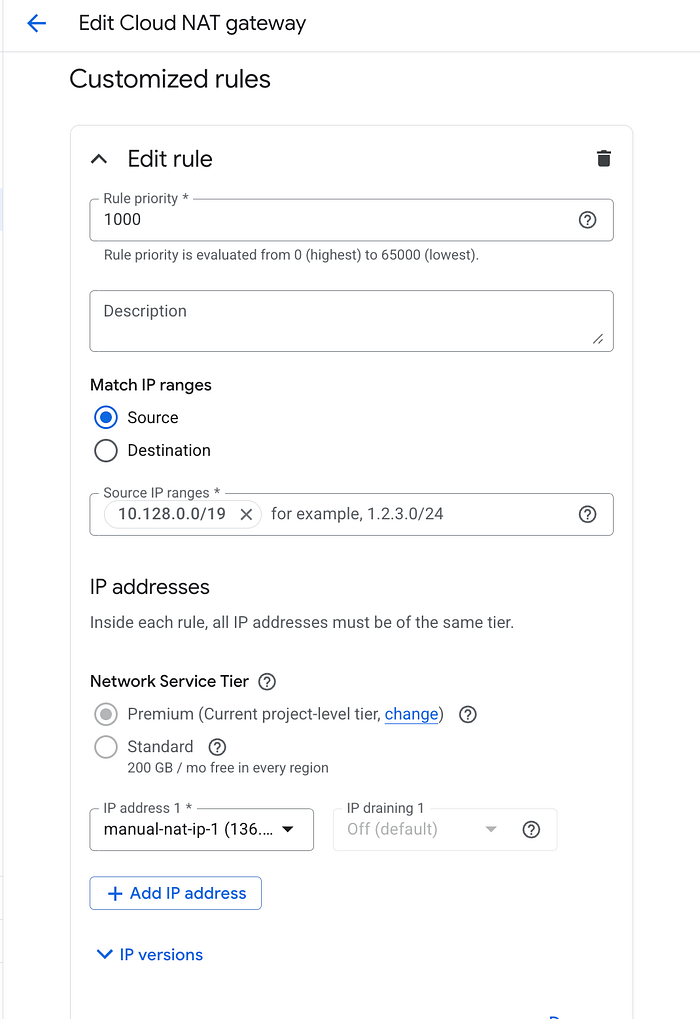
Sample source-based rules
Destination-Based IP Whitelisting: This is the most common and powerful application. In destination-based rules, packets are matched by their destination IP address.
“IF the destination IP is within the
198.51.100.0/24range (our partner's API), THEN use the dedicated public NAT IP203.0.113.20."
This ensures that only specific public IPs are used for whitelisted services, with all other traffic defaulting to the NAT IP pool. It solves the whitelisting issue without compromising general connectivity.
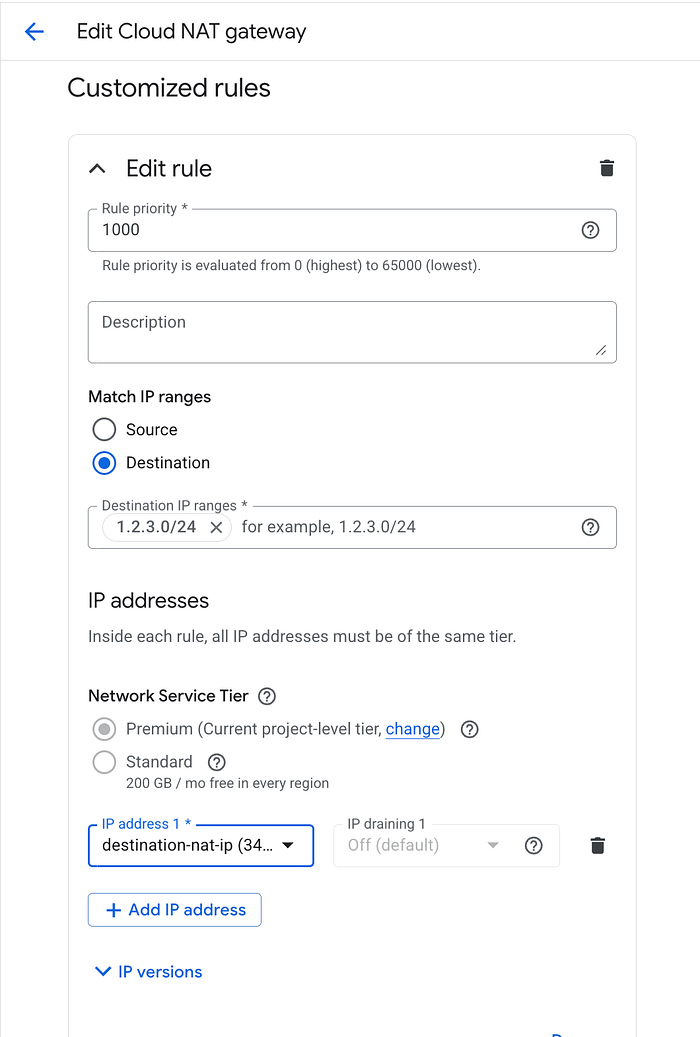
Sample destination-based rules
Enhanced Control and Flexibility
Rules introduce a priority system, allowing network administrators to define policies with precision, ensuring that the most specific and critical rules are evaluated first. This introduces a policy-driven, declarative approach to managing outbound access for privately addressed resources.
Configuring NAT Rules
To use NAT rules, follow these general steps:
- Ensure your NAT gateway is using manual IP allocation (rather than automatic).
- Disable endpoint-independent mapping, since it is incompatible with NAT rules.
- Define your rules, giving them a priority, specifying whether they match by source or destination, and indicate which external IPs to use. .
- Deploy rules via the Cloud Console,
gcloudCLI, or IaC tools. - Monitor, update, or delete rules as your policies evolve.
Minimal gcloud example (source-based rule):
gcloud beta compute routers nats rules create 1000 \
--router=MY_ROUTER \
--region=MY_REGION \
--nat=MY_NAT \
--match='inIpRange(source.ip, "10.10.1.0/24")' \
--source-nat-active-ips=EXTERNAL_IP_1 \
--project=MY_GCP_PROJECT
You can similarly update or delete rules using gcloud compute routers nats rules update/delete commands.
Best Practices
- Carefully design priorities to avoid unintended overlaps.
- Always define a default fallback rule, ensuring coverage for unmatched traffic.
- Monitor active ports and NAT capacity to prevent exhaustion.
- Audit regularly to confirm that rule-based segmentation aligns with compliance requirements.
Cloud NAT rules extend Cloud NAT from a simple IP translation service into a policy-driven control plane for outbound connectivity. By enabling source- and destination-based decisions, they deliver the segmentation, auditability, and compliance that modern cloud environments demand.
When designed thoughtfully, NAT rules transform one-size-fits-all NAT into a flexible, transparent, and secure system — tailored for enterprise-grade networking.
If you are evaluating this for a proof of concept or planning deployments, DoiT can help. Our team of 100+ experts specializes in tailored cloud solutions, ready to guide you through the process and optimize your infrastructure for compliance and future demands.
Let’s discuss what makes the most sense for your company during this policy enforcement phase, ensuring your cloud infrastructure is robust, compliant, and optimized for success. Contact us today.