
At DoiT we help our partners architect and design for scale and for operational excellence. One of the topics we help customers with is planning their network architecture for future growth thus delivering the true promise of the cloud.
Standalone VPC Architecture
Standalone VPCs are isolated network environments that operate independently within a cloud account or project. Each VPC maintains its own networking configuration, security rules, and routing policies, making it ideal for scenarios requiring strict isolation or simple networking requirements.
Key Characteristics
Each standalone VPC maintains complete network isolation from other VPCs, operating as a self-contained environment with its own dedicated networking resources. Network configurations, including routing tables and access controls, are maintained independently, allowing for customized networking policies based on specific workload requirements.
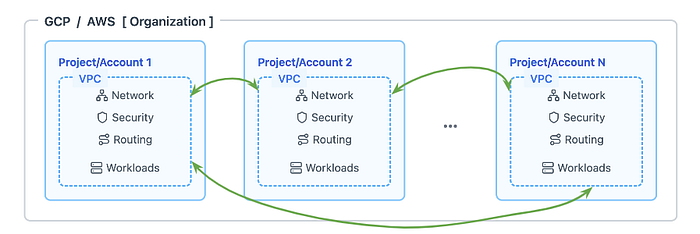
Standalone VPCs are connected with peering as network connectivity requirements dictate, up to a full service mesh (all VPCs are connected to each other)
A standalone VPC architecture is particularly well-suited for organizations with simple applications that have straightforward networking requirements and don’t require extensive cross-network communication. It excels in development and testing environments where isolation is crucial for preventing interference between different environments. Organizations with specific compliance requirements often choose standalone VPCs to maintain complete network separation for sensitive workloads. Small organizations with limited cloud resources and straightforward architectures benefit from the simplicity and clear boundaries of standalone VPCs.
Drawbacks
The independent nature of standalone VPCs often leads to significant resource duplication across different environments, resulting in higher operational costs and maintenance overhead. Organizations face increased complexity when attempting to establish connectivity between multiple VPCs, often requiring complex peering configurations or multiple connection points and possibly NAT solutions to handle CIDR overlap. As the organization scales, managing multiple standalone VPCs becomes increasingly challenging, particularly when implementing consistent policies across environments. The lack of centralized management capabilities makes it difficult to maintain standardized security policies and networking configurations across multiple VPCs.
Shared VPC Architecture
Shared VPC in Google Cloud and AWS (VPC Sharing on AWS) enable organizations to establish a common network infrastructure that can be used across multiple projects (or accounts, for AWS). This approach provides centralized network management while maintaining project-level isolation and security.
Key Components
The Shared VPC architecture is built around a host project that contains and manages the shared VPC network infrastructure. Service projects consume this shared network while maintaining their own resource management and access controls. Subnets can be shared selectively with specific projects, allowing for precise control over network resource allocation. Firewall rules are managed centrally but can be customized for individual service projects when necessary.
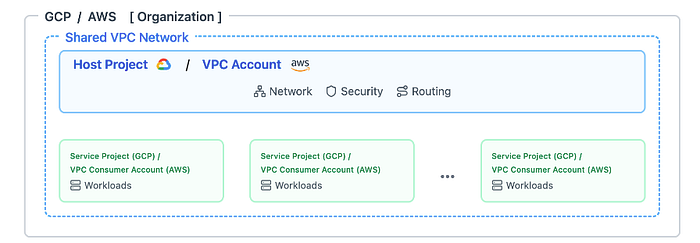
VPC is created in one project and consumed by other projects
Google Cloud Shared VPC vs AWS VPC Sharing
While naming is similar and the core functionality of sharing network resources between cloud projects is included in both, the Google Cloud Shared VPC supports hybrid connectivity (e.g. connections to on-premise hosts) out-of-the-box — by having a hybrid link on the Host project (e.g. Cloud VPN tunnel to on-premise environment), access to the remote location can be granted on each of the Service projects. AWS VPC Sharing on the other hand require additional networking components to be deployed. One such component is the AWS Transit Gateway which we’ll discuss below.
AWS Transit Gateway
While AWS VPC Sharing focuses on sharing subnets from a single VPC across accounts, Transit Gateway facilitates connectivity between multiple VPCs, VPNs, and Direct Connect gateways, making it suitable for complex, multi-VPC networking scenarios or hybrid cloud architectures.
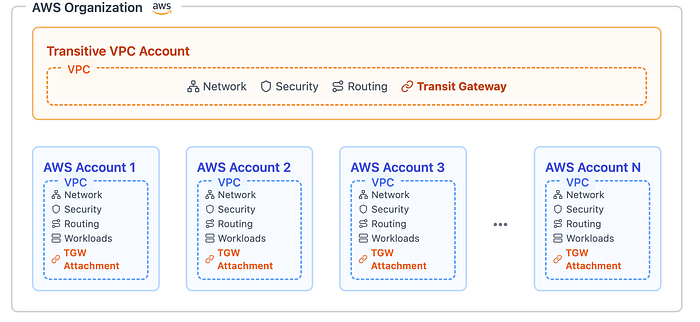
Each AWS account can have one or more VPCs, they can all be connected via the Transit Gateway
We hope this article can help you navigate the web of network architectures with ease. We invite you to read more about our areas of expertise at https://www.doit.com/services/